[\[EN-ReadMe\]](https://github.com/Sugobet/API_Sword/blob/main/%5BEN%5D-README.md) <------ please read this
WeChat Official Account: APT250
Adhering to the principles of open source supremacy and communication learning, API Sword will be open-sourced and simultaneously launched on the official Burp plugin store BApp Store two weeks later (after September 7), facilitating everyone's future updates and usage. It is currently under official code review, and we believe it will be available on the BApp Store soon.
[New Classic Burp Plugin] API Sword - Fully Automatic Deep Collection of APIs in Various Responses
The jar package is in the release; after being listed on the official Burp plugin store, it can also be downloaded from the store.
Preface
This plugin combines my recent work content and some experience from the $40,000 bounty Microsoft account vulnerability API.
Developers using API Sword have repeatedly achieved results and general 0days in projects. With this tool, I no longer painfully search for any interfaces, paths, or parameters manually from any JS.

Similar to many popular JS Finder, URLFinder, and other related JS and API mining tools, they are excellent tools, and API Sword gains capability and advantage thanks to Burp's features.
Screenshot of the plugin main page:
Main Features of API Sword
API Sword is fully automatic with loop prevention, extracting APIs and JS files within the specified range from various responses, then recursively deeply extracting APIs, actively requesting APIs, JS, and other valuable files.
The API results are WYSIWYG; the right window shows the source JS of the API, allowing you to immediately get API parameter information from the JS, then Burp can jump over with ctrl + r for testing.
It is not as complicated as imagined; what API Sword does more is reducing a large amount of repetitive, time-consuming, and tedious JS, API, and API parameter searching work for us.
- API Sword captures traffic within the scope passing through Burp and extracts the vast majority of links from HTTP responses.
- API Sword cleans any links and paths extracted in the previous step, then judges and actively initiates GET and POST requests to APIs, JS, etc.
- API Sword further processes the responses of the active requests from the previous step, continues extracting information from the responses, and repeats the previous step's actions. API Sword has a loop prevention feature, so no need to worry about infinite request loops.
- API Sword pushes all qualified API requests, responses, and the JS file responses that source the API interfaces to the API Sword Burp GUI.
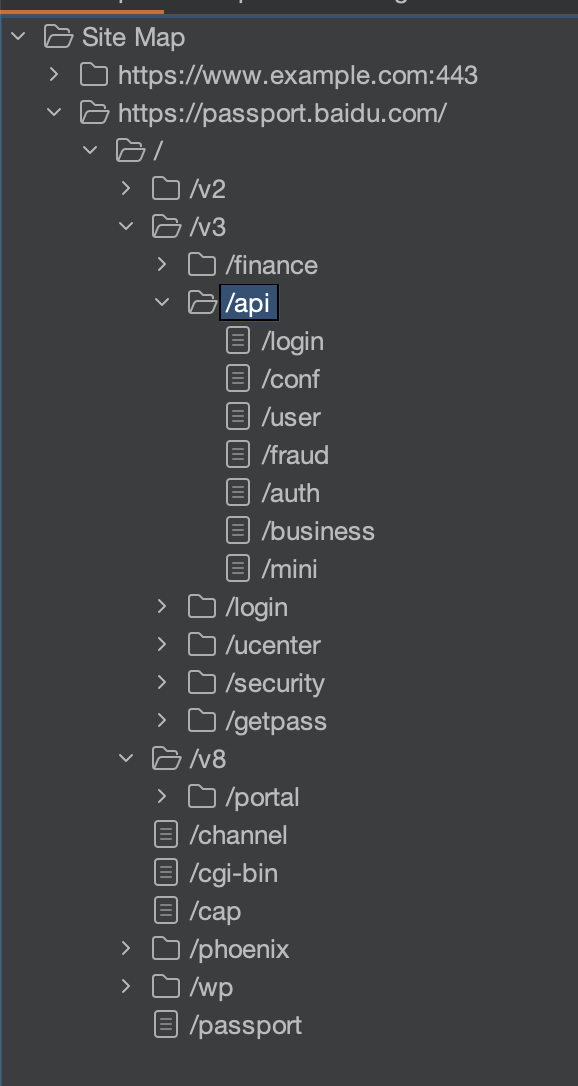
- API Sword automatically adds all related requests to Burp's target sitemap. You can fully enjoy the fruits brought by API Sword in the target sitemap's analysis and other functions.
Considering opsec and other operational security risks, API Sword currently does not actively fuzz parameters. If there is demand later, this will be added as an optional feature.
How to Use?
Note: The plugin requires Burp Suite version 2024.7 or above; (for versions below 2024.7, you need to manually turn off the "Use Original Headers" feature on the plugin's settings page)
Using the API Sword is very simple,
- Install the plugin into Burp version 2024 or later, ensure the plugin has no errors
- Set the Scope for the plugin
- Open the browser and ensure the browser traffic goes through Burp
- Visit the target website, click and test anything you see on the site
- After a while, check the fruits from the API Sword's Sitemap
API Sword Settings
In the Scope tab, we can set the range, which can be URL, domain name, or IP
This scope is especially important, it is recommended to consider carefully, otherwise you might easily scan outer space.
After setting the scope, let's look at the Setting tab
- Allow active API requests
- Use original headers
- Immediately stop sending all requests
- Clear all data in the current SiteMap
- Enable active HTTP request rate
- Whether to additionally add a custom path request during active requests
- Filter out custom response codes that are not 200
- Allow API Sword to actively search for baseURL from the response and actively concatenate paths to the baseURL
- Add custom header fields: (automatically overwrite existing header fields)
- Enable bypass of dangerous interface access (skip if the interface contains certain strings)
- Save scope and all settings
- Whether to add an extra custom path after the API interface and before the parameters
- Thread count control
Acknowledgments
Thanks to Microsoft
Thanks to my NSFOCUS mentor
Thanks to mil1ln
Thanks to Tanjie
Thanks to everyone who provided valuable opinions and feedback for API Sword during the testing phase
Thanks to all the above for all the support provided to API Sword!
TODO
- Collect a plum blossom K polo shirt ⬛️
- Add optional base URL path fuzzing ✅
- Add custom response code filtering ✅
- Add option for custom base path when API Sword actively requests ✅
- Optimized matching strategy, unlocking 80% of API Sword performance ✅
- API Sword active request optimization to avoid accessing dangerous APIs ✅
- Fixed the issue where Burp's default header does not carry the CT field ✅
- Optimized tags width in the response table ✅
- Fixed UI flickering issue of sitemap ✅
- Added optional custom request headers feature ✅
- Added automatic sorting of tags in the response list ✅
- Optimized matching strategy ✅
- Optimized code blocks ⬛️
- Registered Burp uninstall handling ✅
- Added bilingual (Chinese-English) readable code comments throughout the code ⬛️
- Added bilingual (Chinese-English) toggle feature in GUI ✅
- Optimized UI to fix Burp lag and rendering issues ✅
- Added save scope and configuration feature ✅
- Added active HTTP request rate control feature ✅
- Added multithreading feature ✅
- Added custom path feature between interface suffix and parameter prefix ✅
- Emergency fix for loop prevention logic failure caused by multithreading ✅
- Fixed display error in auto sorting ✅
- Optimized API list UI; arrow keys no longer interrupt input when inserting data ✅
- Thoroughly fixed the bug where loop prevention logic still failed due to multithreading ✅
- Added filter feature ✅
- Added expand nodes and collapse all nodes feature ✅
- Optimized clear site map feature ✅
- Optimized js concatenation logic in CDN | cross-site to use referer as baseUrl ✅
- Added manual scanning feature; manual scanning will auto add host to scope list: right-click on a request body in Burp -> Extensions -> API Sword -> API Scan ✅